Protect your digital infrastructure: Vulnerability management as the key to cybersecurity. Learn how to identify security gaps early on and neutralize them in a targeted manner.
What is vulnerability management?
Digital security is like a chain—it is only as strong as its weakest link. In the complex world of IT systems, this means that every undetected vulnerability can become a gateway for cybercriminals.
Vulnerability management is the strategic key to systematically identifying, prioritizing, and neutralizing these vulnerabilities. It is more than just a security measure—it is a proactive protection strategy that makes your entire IT infrastructure resilient.
The consequences of neglecting vulnerability management are dramatic: from data theft and massive business interruptions to financial losses that threaten the very existence of a company. Companies without effective vulnerability management are literally playing roulette with their digital security.
Why do I need vulnerability management?
Proactive vulnerability management is your strategic line of defense against cyber threats—it's no longer just about reaction, but about proactive protection. Regular, systematic checks of your IT systems are not optional, but essential for survival. Every undetected vulnerability is like an open back door for cybercriminals – and they will seize every opportunity to break in before you can close it.
Well-designed vulnerability management does more than just plug holes. It transforms your IT infrastructure into an adaptive, resilient protective zone that neutralizes potential attacks before they even begin. The goal: prevention rather than repair—preserving invaluable resources such as company data, reputation, and trust. The advantages are clear:
- Proactive protection against cyberattacks
- Minimization of financial risks
- Protecting the company's reputation
- Strengthening customer confidence
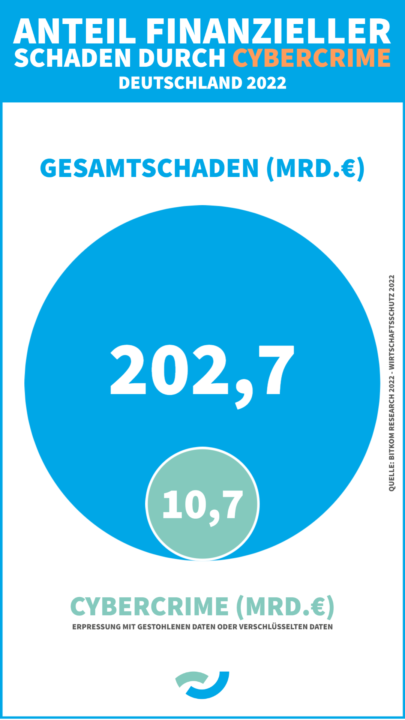
In 2023, several German companies and institutions have already fallen victim to cybercrime, including Stadtwerke Karlsruhe , Bayerischer Rundfunk and Hamburg Airport . The industry association Bitkom e.V. estimates the damage caused by cyber attacks in 2022 at €10.7 billion.
These examples clearly show why vulnerability management is so important in IT. If vulnerabilities are not identified and remedied in a timely manner, they can lead to serious security issues and have a significant impact on the organizations affected. It is therefore crucial to implement best practices in vulnerability management in order to identify and remedy vulnerabilities as quickly as possible before they can be exploited.
How do you implement (active) vulnerability management?
- Regular review of the IT infrastructure Regular reviews of IT systems, networks, and applications are crucial for companies in order to identify vulnerabilities. It is important that these reviews are carried out both automatically and manually.
- Once companies have identified vulnerabilities in their IT systems, networks, and applications, it is important to prioritize them according to their severity and risk. This allows companies to ensure that vulnerabilities that pose a high risk are given priority.
- Process automation Automated processes make it easier to quickly and effectively identify and fix vulnerabilities in the IT system. Vulnerability scanners, patch management tools, and other automated security solutions can be used for this purpose.
- Employee training Companies should ensure that their employees are aware of the importance of vulnerability management and are able to identify security risks. Employees should also be trained to ensure that they take the right steps to report and fix vulnerabilities.
- Implementation of patch management strategies To ensure that vulnerabilities can be remedied quickly and effectively, it is advisable to implement an effective patch management strategy.
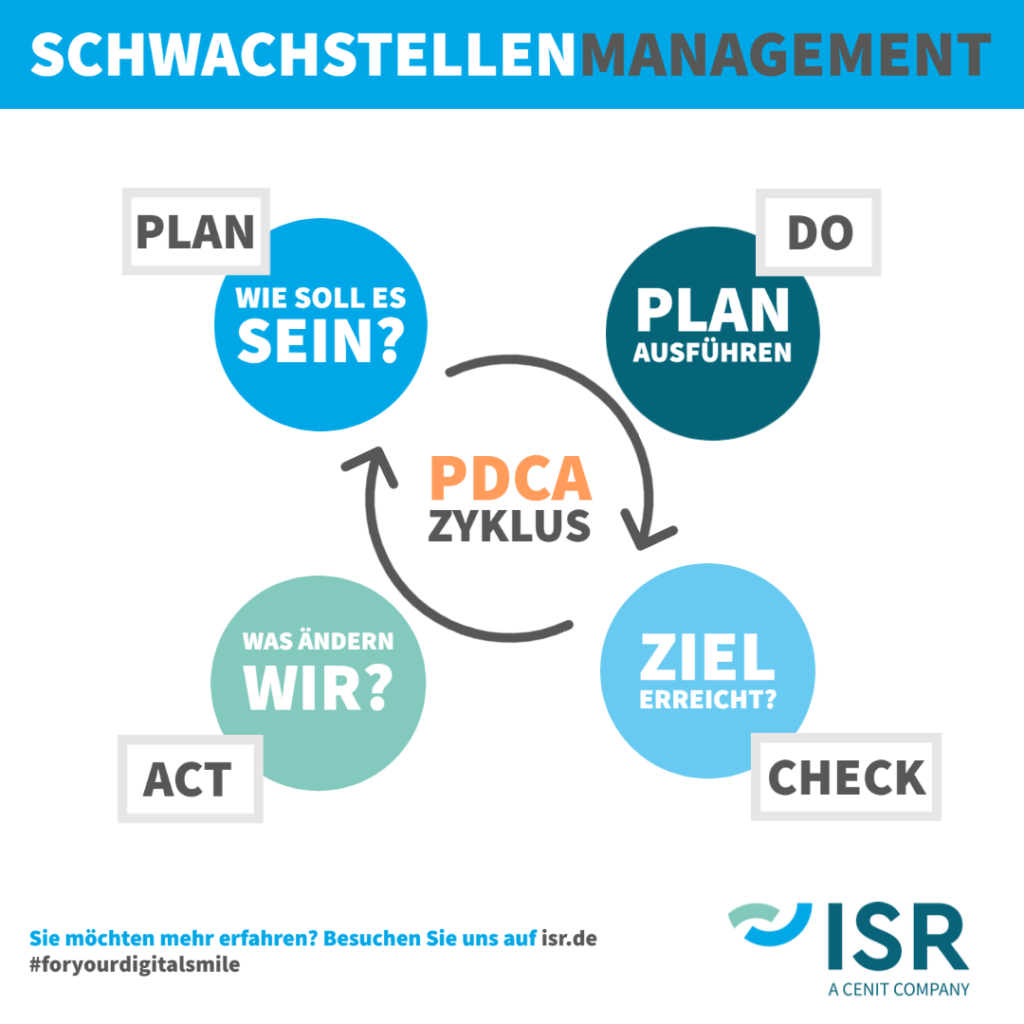
These five steps provide a good basis for identifying, evaluating, and remedying weaknesses. To make this process even more effective, the PDCA model can be applied. The PDCA cycle essentially draws on the principles described above and consists of four steps: Plan, Do, Check, and Act.
The PDCA cycle in practice
A good example of the application of the PDCA cycle is the implementation of firewalls in a network.
During the planning phase, goals and strategies for improvement are defined. It must be determined what type of data traffic should be allowed through and what should be blocked. The firewall configuration is created according to these requirements.
In the second step, the "Do," these plans are implemented. In the case of our firewall example, the hardware is installed and the software is tailored to the specific requirements of the network. It is important that during this phase, the firewall is tested by an expert to ensure that it is functioning properly.
In the third phase, "Check," the effectiveness of the measures taken is monitored and the results are compared with the goals set in the planning phase. This means that the firewall is constantly monitored to ensure that it is functioning correctly and that all requirements are being met.
Finally, in the fourth phase, "Act," improvements are made to further optimize the vulnerability management process. This means that the performance of the firewall is constantly evaluated and improvements are made where necessary. This also includes checking for security gaps and vulnerabilities that may arise. New requirements can also be added to ensure that the firewall can withstand changing threats.
Overall, the PDCA cycle is an important method for ensuring that the implementation of IT security measures is effective and continuously improved.
Vulnerability management in action!
At ISR, we attach great importance to regularly reviewing and improving both our products and our internal processes. Vulnerability management is an integral part of our ISO 9001-certified quality management system.
This is precisely why, as an IT service provider, we can support companies in planning and implementing vulnerability management strategies, e.g., in the area of software monitoring and software maintenance. This allows potential vulnerabilities to be quickly identified and remedied. With our knowledge and experience, we support your internal IT and help your company focus on its core competencies and business.
In June last year, a leading Hessian company in the sports sector suffered a widespread hacker attack using ransomware. This restricted access to large parts of the IT infrastructure. As ISR was working there as an analytics service provider, we responded immediately and helped the affected customer as quickly and comprehensively as possible to defend against the attack and repair the damage.
And patch management? – Of course!
As an external IT service provider, we at ISR also support your company in another important aspect of vulnerability management—patch management. patch managementPatch management is the implementation of measures to maintain the.... We provide regular updates and patches for our customers' software and systems to close security gaps and keep the IT infrastructure up to date.
To provide you with the best possible patch management support, we implement automated tools and processes that ensure updates are installed promptly and efficiently. We draw on our experience and best practices to ensure that patch management is carried out in line with your company's requirements.
We help you to protect and optimize your IT systems and applications in the best possible way. By outsourcing patch management, you can concentrate on your core competencies and rest assured that your IT systems are always up to date and protected against security threats.
If you would like to learn more about what we offer in this area or about our products and services, please contact us directly. We look forward to hearing from you.

Jens Brettschneider
Head of Business Unit
Application Management
jens.brettschneider@isr.de
+49(0)151 422 05 425